
Have you ever received an SMS claiming that you won £1,000,000 in the national lottery? Or did you get an email from a friend claiming that he’s stranded in a foreign country and needs you to send them money to help him get home? In most cases this is the work of ‘phishers’ trying to get access to your personal information.
What is phishing?
‘Phishing’ is an attempt to get you to hand over personal, confidential information to a criminal. The requests may seem legitimate and may be perpetrated by phone, email, via the Internet, or even in person. The danger lies in the fact that these phishing attempts look legitimate – sometimes even carrying an official-looking logo – and con you into providing information to fraudsters that you would not normally give to anyone else.
Phishing strategies

Phishers use different methods to trick people, so it’s wise to always be cautious. For example, you may get a phone call from a company saying that there is a virus on your PC and that you can pay them a fee to remove it and keep it clean thereafter.
More often, phishers use email as the route of attack. Phishers often use information that will make you take note of the email and react. They may say that your bank or email account has been hacked and that you need to verify your details by sending them your username and password/PIN, or ask that you click on a link. Or they may try to fool you into thinking you’re the latest millionaire in a sweepstake competition. You are then required to send them your banking details so that they can deposit the money into your bank account.
You may even receive an email from your mobile service provider asking for your personal information to update their records. These are common tell-tale signs of phishing attempts and you need to be extra vigilant when you are asked to provide your personal information.
A legitimate company will never ask you to verify your account information, passwords, security questions, or other sensitive information. So if you receive a suspicious email, delete it immediately.
Verifying the message
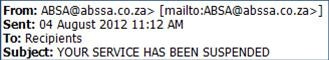
If you are unsure about a message’s authenticity, check the email header – which shows you the From, To, and Subject information. In most cases, there are either spelling mistakes, or the message isn’t even from the company referred to in the email. Also, phishing messages are often badly-written – using poor English, which indicates that the legitimate company did not send you the message.
Another way to check on the message is to contact the real company’s customer service and ask about the call or email you received.
Precautions against phishing
Use the following tips to make sure that you are not caught hook, line and sinker by a phishing attack.
- If an email asks you for personal information, never click on any links within that email.
- Beware of pharming which is when a hacker redirects a legitimate website’s traffic to a bogus site. Malware or a virus takes over your web browser and when you try to access a legitimate website you’ll be directed to a fake one. Once you provide your personal information on the site, hackers can access this information and fraudulently use it.
- Never enter your personal information on a pop-up screen.
- Use antivirus software. (UCT users can install McAfee antivirus on campus and at home.)
- Only open email attachments if you’re expecting them or know what they contain.
- Be cautious when accepting telephone calls where the caller asks you to provide or verify personal information.
- Always verify the caller’s identity. Some phishers call you claiming you’ve been a victim of some sort of crime, while others may pretend to be a prospective employer who would like to hire you but needs you to verify your information.
- If you’ve been hooked by a phisher, contact your bank or agency and inform them that your account has been hacked. You should also let them know if someone has been impersonating their business.
- If you receive an email from a company requesting a reply and the email address looks legitimate, contact the company’s customer service informing them about the email you received. Never reply to the email.
- Be wary of any emails claiming that there has been a breach of security on your account and they company needs you to submit personal information.
- If you unsure of an unsolicited email, rather delete the message.
- Always check the email address the email was sent from. In most cases there are either spelling mistakes or it isn’t even from the so called company.
- Check to see if there any numbers in a web address e.g. http://123445.www.companyname.com, as this could be a fake website.
- Most legitimate companies will not use words like “verify” in their web address. Always double check the web address before entering any personal information. If you are still unsure then search for the company online and compare the web address in the email to the one in your browser.
